What is Application Security Assessment?
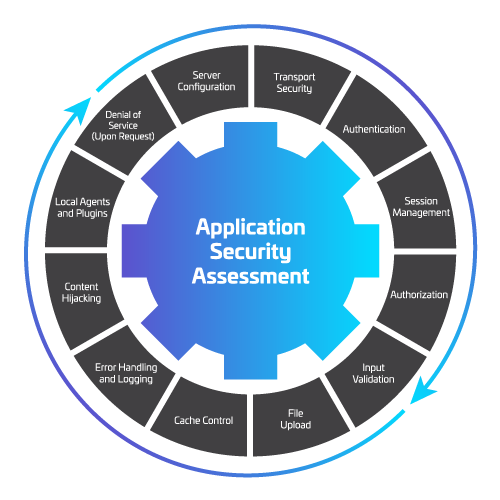
An application security assessment is a comprehensive evaluation of the security aspects of a software application. It involves identifying and mitigating potential security vulnerabilities and weaknesses that could be exploited by attackers. The assessment aims to ensure that the application is robust against various security threats and meets industry standards.
During an application security assessment, security experts analyze the application's code, architecture, and configuration to uncover security risks. This process helps organizations enhance the security posture of their applications, protecting sensitive data and preventing unauthorized access.
Get in Touch